Many people at HKUST have at some time received an email message with a subject or message along the lines of “HKUST Webmail Upgrade” or “Your Mailbox is almost full”. Subject lines coupled with a spoof (fake) return address, such as “Administrator@ust.hk”, “Helpdesk@ust.hk”, or “AccountsDept@ (your bank).com” can catch out the unwary. In addition, these messages often contain logos and trademarks that look legitimate to further confuse recipients.
When trying to determine if you have received a phishing email, remember that no legitimate company will ever send you an email requesting your username, password, or any other personal identification information.
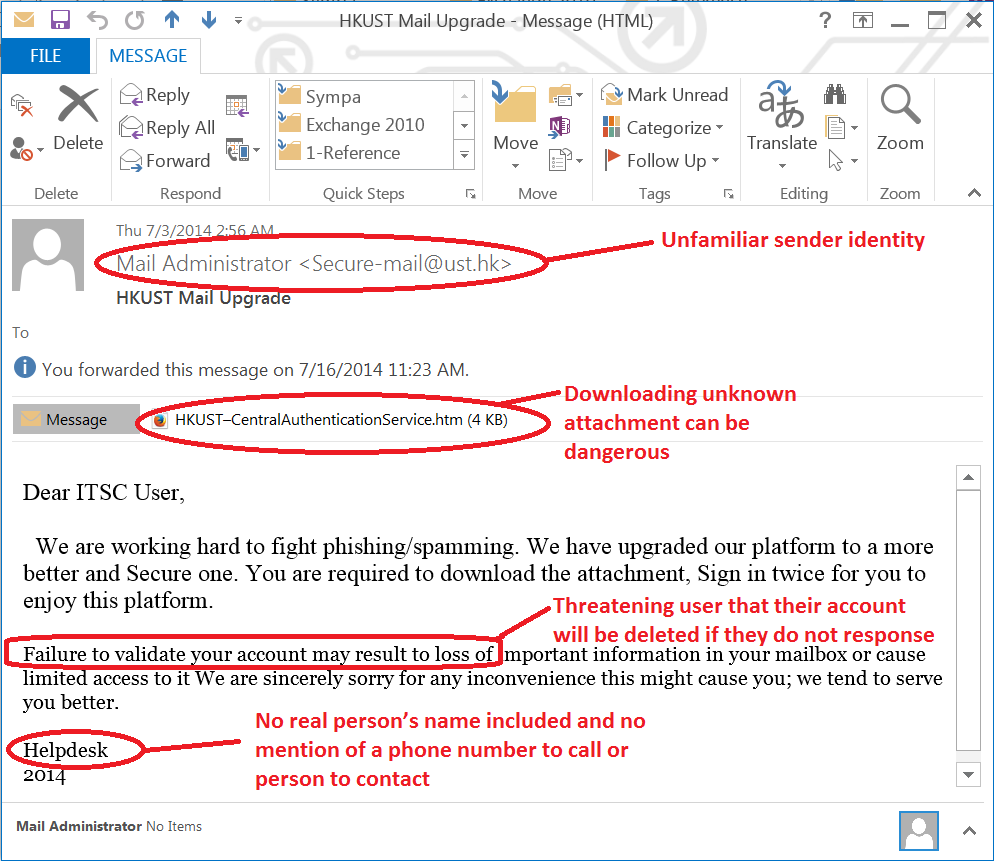
- Unfamiliar sender identity e.g. mail administrator or spoof identity (sender’s identity cannot be verified, i.e. not signed).
- A request of your password.
- A threat that your account will be deleted if you do not respond to lure you into providing your account / password.
- A return or reply-to email address that is a spoof. View the “full header” to see the actual return address.
- Spelling errors and bad grammar.
- Odd formatting (e.g., incorrect use of capital letters or punctuation).
- No real name included in the greeting or signature.
- No mention of a phone number or person to contact.
- Includes attachments and asks you to download them.
- Includes a hyperlink with an odd URL (e.g. a foreign country as the domain) or tries to match a legitimate web address but is spelled differently (e.g. microsoft.com vs micosoft.com).
Phishing Email Using a Fake Login Page
Emails from spoof addresses, such as supports@ust.hk or webmail@ust.hk, ask HKUST members to confirm their email accounts by supplying their username and password, or to click on a malicious link. Never reveal your password to anyone. ITSC will never ask you for such information by email, phone or in person. No staff member will ever ask for your password either.
Below are screen shots of a valid HKUST SSO login page:

For legitimate websites, always check if the connection is secured (https://) or not.
You can also view other phishing examples to familiarize yourself with tactics employed by spammers.