What is a Social Engineering Attack?
In this situation, an attacker uses human interaction, such as social skills, to obtain or compromise information about an organization or its computer systems. An attacker may sound plausible, perhaps even claiming to be a new member of staff/student, or researcher and even offering credentials to support that identity. However, by asking questions, the attacker may be able to piece together enough information to infiltrate an organization’s network. If an attacker cannot gather enough information from one source, he or she may contact another source within the same organization and rely on information from the first source to boost credibility.
What is a Phishing Attack?
Phishing is a form of social engineering. These attacks use email or malicious websites to lure people into providing personal information/account details. When users respond, attackers can use the information provided to gain access to accounts. Visit Phishing Examples to see what has been reported in the past.
Phishing attacks may also appear to come from other types of organizations, such as charities. Attackers often take advantage of current events and certain times of the year, such as:
- Natural disasters (tsunami, etc)
- Health scares (COVID19, etc)
- Financial deceptions (payroll, lottery scams)
- Holidays (online shopping scams)
Tips to Avoid Email Phishing
1. Beware of Spoof Emails or Email Phishing
click to enlarge the following image
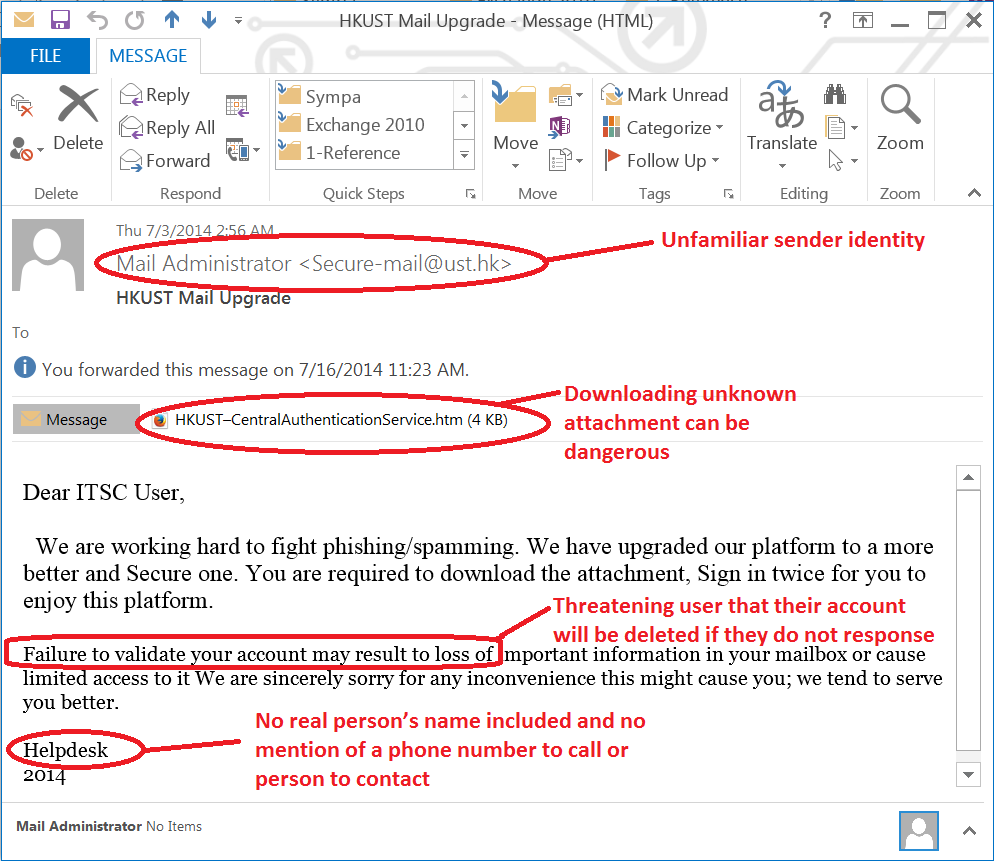
Spammers and malicious advertisers often use a fake identity (either a real or non-existent email address) to send spam messages or messages with viral attachments. Identity thieves may also try to lure you into surrendering personal information by falsely claiming to be a legitimate enterprise in their phishing message or diverting you to a fake website, which looks identical to the genuine one.
If you suspect that you have received a phishing email, do not respond or click on the links. Visit Spotting a Phishing Email to find out ways to assess a message.
2. Try to recognize genuine senders
Sometimes it is difficult to recognize if an email comes from a genuine sender by looking at the “from address” or the message context. If in doubt, ask for additional confirmation to verify the identity of the sender. A better way is to use digital signature technology to give recipients confidence that the messages are genuine. Digital signature technology, based on a digital certificate (i.e. e-Certificate), has been used on campus for nearly a decade.
All University members can use an e-Cert to digitally sign outgoing messages. Such “signed” messages (carrying an  icon in Microsoft Outlook or Outlook on the web), give immediate assurance about the identity of the sender.
icon in Microsoft Outlook or Outlook on the web), give immediate assurance about the identity of the sender.
3. Don’t open unexpected attachments
Viruses are often sent via email attachments. The campus network’s email firewall scans incoming email and blocks known viruses. However, new viruses may get through before the latest virus signatures are available. Please note that neither ITSC nor software vendors, such as Microsoft, will send system patches as e-mail attachments. Instead, you will be asked to download the required software from their websites. In general, don’t open an attachment unless you are expecting it.
4. DON’T send sensitive personal files or financial information in email
When you send a message, you no longer have control over what is done with it or to whom it is forwarded. Do not send sensitive data in email as it is unsafe.
5. Don’t send sensitive information over the internet before checking a website’s security
A secure site should begin with https:// together with a closed padlock 
6. Avoid clicking on links in the body of an email
Those links may not be a phishing attempt, but they may not go to the site you intend. Unless you are completely comfortable that the email is legitimate, it is best to copy and paste the link or type it directly into your browser.
Check whether the spelling of the site is correct. For example, microsoft.com vs micosoft.com. You can check the URL in any email or website by holding your mouse above the link. The URL will appear in your browser or status bar (usually at the bottom of your screen) so you can see the site’s name before you click on it.
7. Install and maintain anti-virus software, firewalls, and email filters
This can reduce email traffic.
8. Maintain your ITSC Network Account password
Don’t forget to change your password periodically.
If You Think You Are a Victim
If you believe you might have revealed sensitive information about HKUST or personal information, report the matter to security@ust.hk as soon as possible to alert ITSC to look for suspicious or unusual activity.
If you believe your financial accounts may be compromised, contact your financial institution immediately and close any accounts that may have been compromised. Watch for any unexplained expenditure in your account.
Immediately change any passwords you might have revealed. If you have used the same password for multiple resources, make sure you change it for each account and don’t use that password in the future. You should also consider reporting the attack to the police.
Useful Resources
To avoid falling for scams, everyone needs to raise their levels of caution. Scammers may use new technologies to find different ways to trick people. All of us should be careful about this. See the Self Help Guide for Security Incidents from HKCERT for more information. The Hong Kong police also provide online information and advice on international fraud.
